What is a Cybersecurity framework? ⚔️
Table of Contents
Every time I publish a post on my blog and provide guidance, I do so with a security framework in mind. This makes my advice more reliable. If followed, it should result in better secure environments.
Field of expertise
Please remember that my primary field of expertise is security, identities, devices, and data within the Microsoft Enterprise Mobility + Security ecosystem. Each of these can be matched to the following technology.
- Security with Microsoft 365 Defender
- Identities with Azure AD
- Devices managed by Endpoint Manager (primary Intune)
- Data stored in SharePoint and Exchange Online
Cybersecurity frameworks adopt a framework-based approach to securing digital assets. The primary purpose of developing cybersecurity frameworks is to provide a variety of high-quality protection and dependable methods for mitigating cyber risk. Cybersecurity frameworks are required to maintain a higher level of security.
A robust framework for cyber risk management is integrated into the firm's risk management strategy and activities. In conjunction with current information technology and artificial intelligence, a powerful framework for cybersecurity risk management may successfully avoid cyber attacks.
Cybersecurity frameworks 🔐
Let me introduce you to the frameworks, but please note that I am not an expert in each of them(which is impossible)! As a techie, I recommend NIST, CIS, and Microsoft's Zero-trust model⭐.
NIST (National Institute of Standards and Technology)
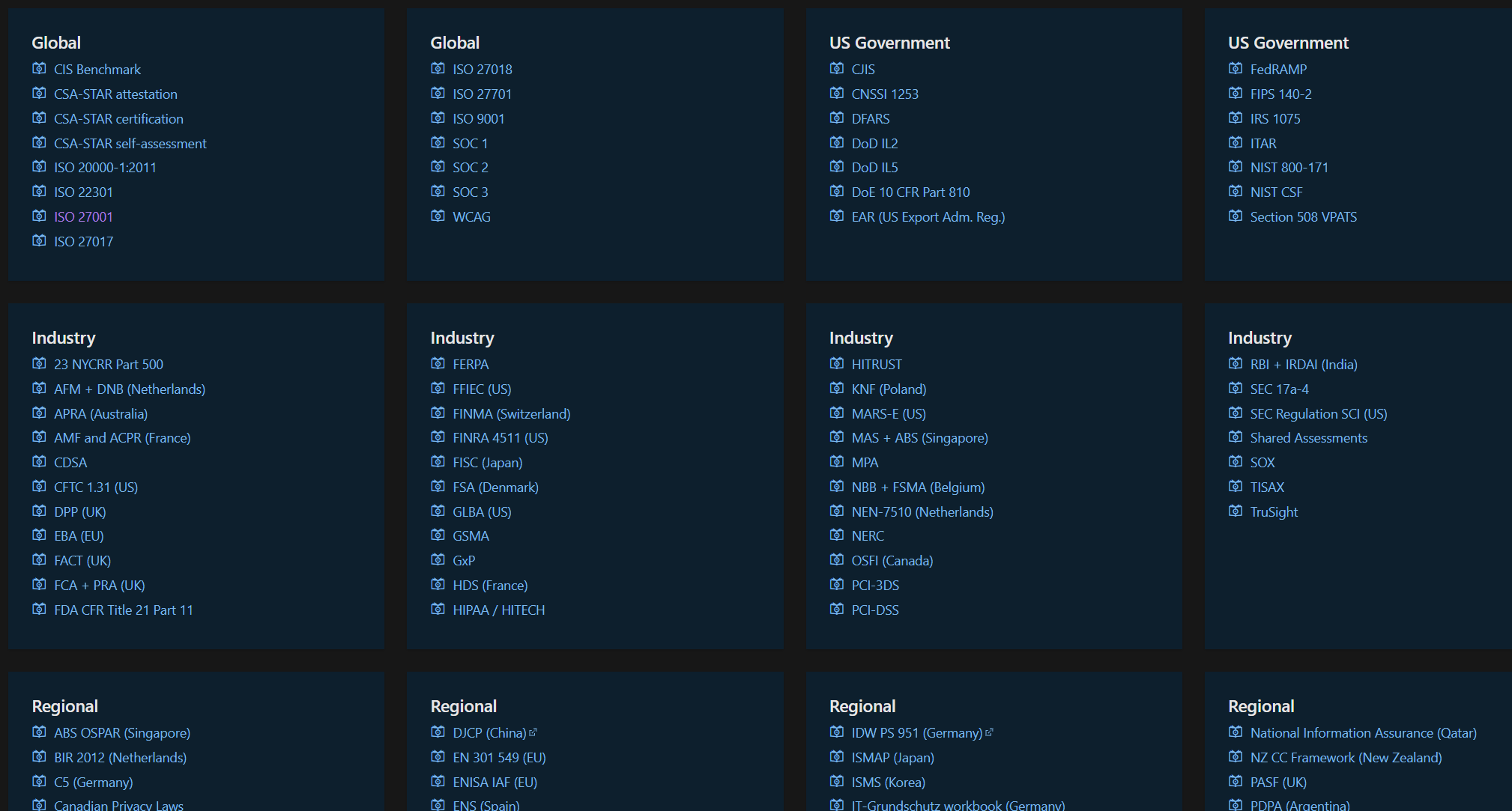
The National Institute of Standards and Technology is shortened to NIST. It is a non-regulatory group that promotes technological adoption and raises standards for American businesses. With the emergence of networks and cybersecurity risks, NIST's role in setting standards and best practices for enterprises has become more crucial.
CIS (Center for Internet Security)
Since 2000, the Center for Internet Security (CIS) has existed. The mission of this group is to assist public and commercial organizations in adopting better cybersecurity policies. This necessitates supporting standardized cybersecurity practices and cultivating communities that can advance cybersecurity research. The CIS' Critical Security Controls (CSC) guidelines are well-known. The CIS CSC guidelines contain twenty measures that organizations can use to enhance their cybersecurity preparedness and response requirements.
ISO (International Organization for Standardization)
ISO/IEC 27001 is a security standard that explicitly describes an Information Security Management System (ISMS) designed to implement explicit management control over information security.
GDPR (General Data Protection Regulation)
The General Data Protection Regulation (GDPR) provides new standards for enterprises who offer products and services to EU citizens or that collect and analyze EU resident data, regardless of location
Zero Trust Model by Microsoft
Zero Trust is the essential security strategy for today’s reality. In 2020, the global pandemic compelled nearly every organization to embrace a Zero Trust strategy as employees went remote, virtual private networks (VPNs) were breached or overwhelmed, and digital transformation became critical to organizational sustainability.
The mandate emerged for a Zero Trust approach to verify and secure every identity, validate device health, enforce least privilege, and capture and analyze telemetry to better understand and secure the digital environment. Governments and businesses worldwide recognized this imperative and accelerated the adoption of a Zero Trust strategy. Through supporting thousands of deployments and observing the expanding threat landscape, we have revised and evolved the Zero Trust architecture and maturity model we released two years ago based on what we have learned. We want to share those learnings for organizations to implement today and tomorrow
More information

https://reciprocity.com/resources/what-is-a-cybersecurity-framework/