Solve MFA fatigue
Table of Contents
If you frequently receive complaints about the number of MFA prompts, or if users begin to carelessly click on notifications, your implementation is incomplete. We are human, and doing the same thing over and over again tires and irritates us. We must take MFA fatigue seriously.
Every time you receive a complaint, you lose interest in innovative solutions and organization-wide support. Would you believe me if I told you that unnecessary MFA prompts actually result in a lower security level than intended?
- Performing multiple button presses
- Repeating the same action over and over
- Lossing interest in what i click
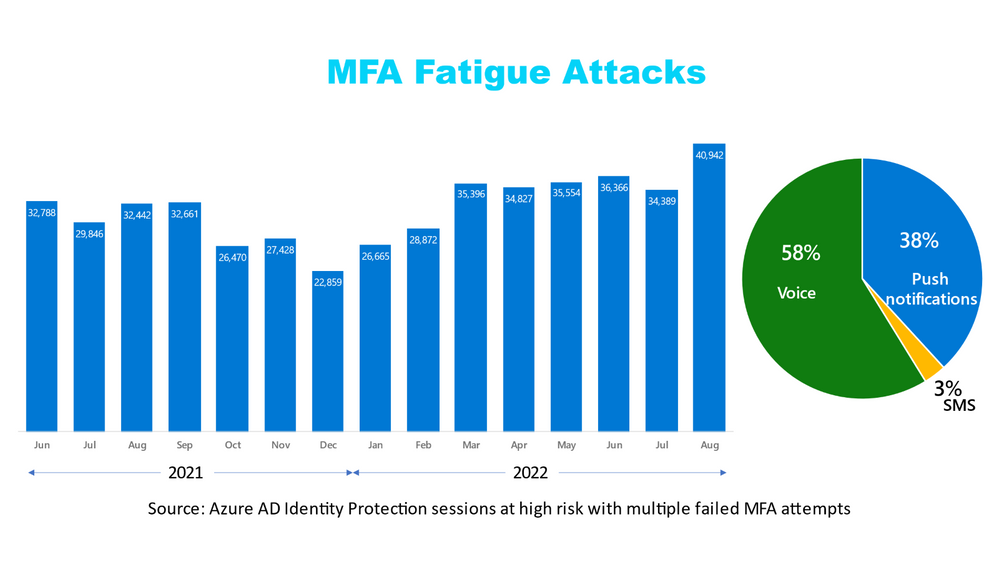
The following image shows the frequency of MFA fatigue attacks, and what I found interesting from it is that we have a serious problem that is only getting worse with time ⚠️.
Human behavior
MFA fatigue is an underrated topic in human behavior, but understanding how our solution will be adopted is one of the most modern topics to date; human behaviors will never be replaced by technology, but will only evolve. We suppress innovation and growth by hardening the playing field with security.
Human behavior is the potential and expressed capacity (mentally, physically, and socially) of human individuals or groups to respond to internal and external stimuli throughout their life.[1][2] Behavior is driven by genetic and environmental factors that affect an individual. Behavior is also driven, in part, by thoughts and feelings, which provide insight into individual psyche, revealing such things as attitudes and values. Human behavior is shaped by psychological traits, as personality types vary from person to person, producing different actions and behavior. (source: Wikipedia)

User perspective
We are nothing without our beloved users who actually use the tool box we manage, but users have been left out in some cases regarding adoption and answers to "what is in it for me?" over the last few years. Users understand that IT security is now a serious matter that is here to stay, but they will lose interest over time because that is just human nature. The simplest way to gain our users' trust is to be both invisible and noticeable.
IT perspective
I can't speak for everyone, but 1-2 years ago, IT security was no longer a topic of discussion, and the more robust security we could put in place, the better we could all sleep at night. But, despite our best intentions, we unknowingly introduced a security risk.
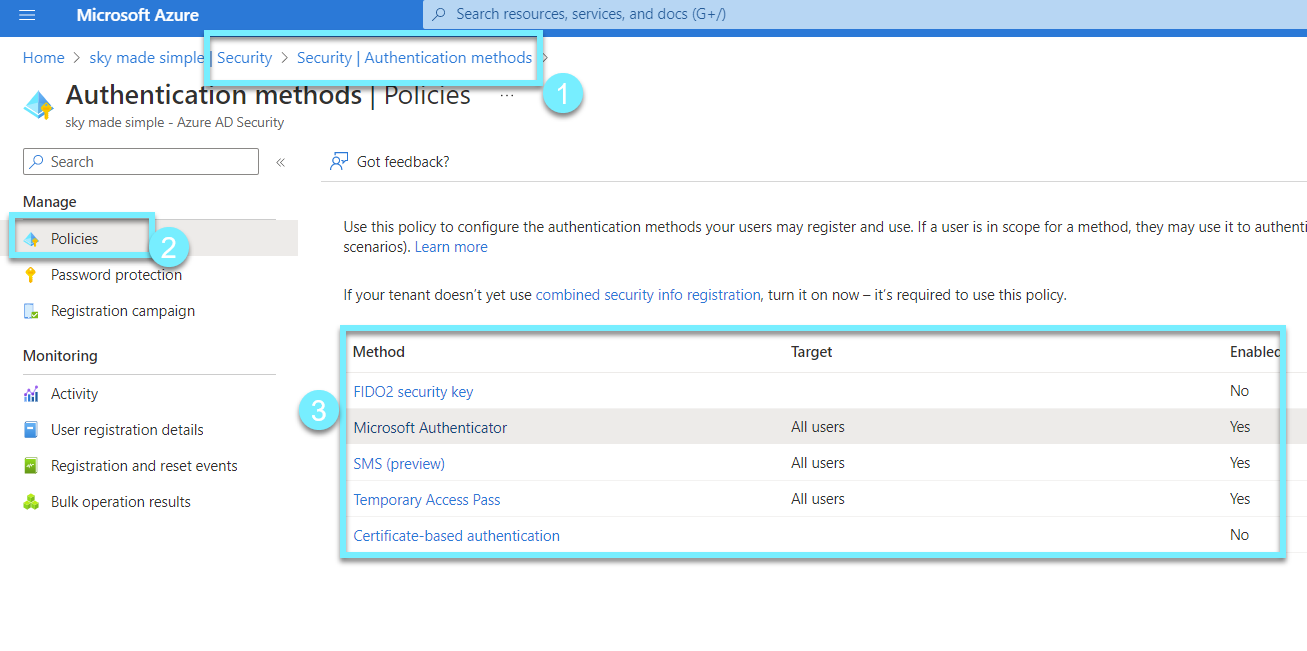
Azure AD Security
Let's head on over to our beloved Security department in Azure AD, in here we can manage our security in Azure AD. What we are going to work with in this posts is the new 🆕 authentication methods.
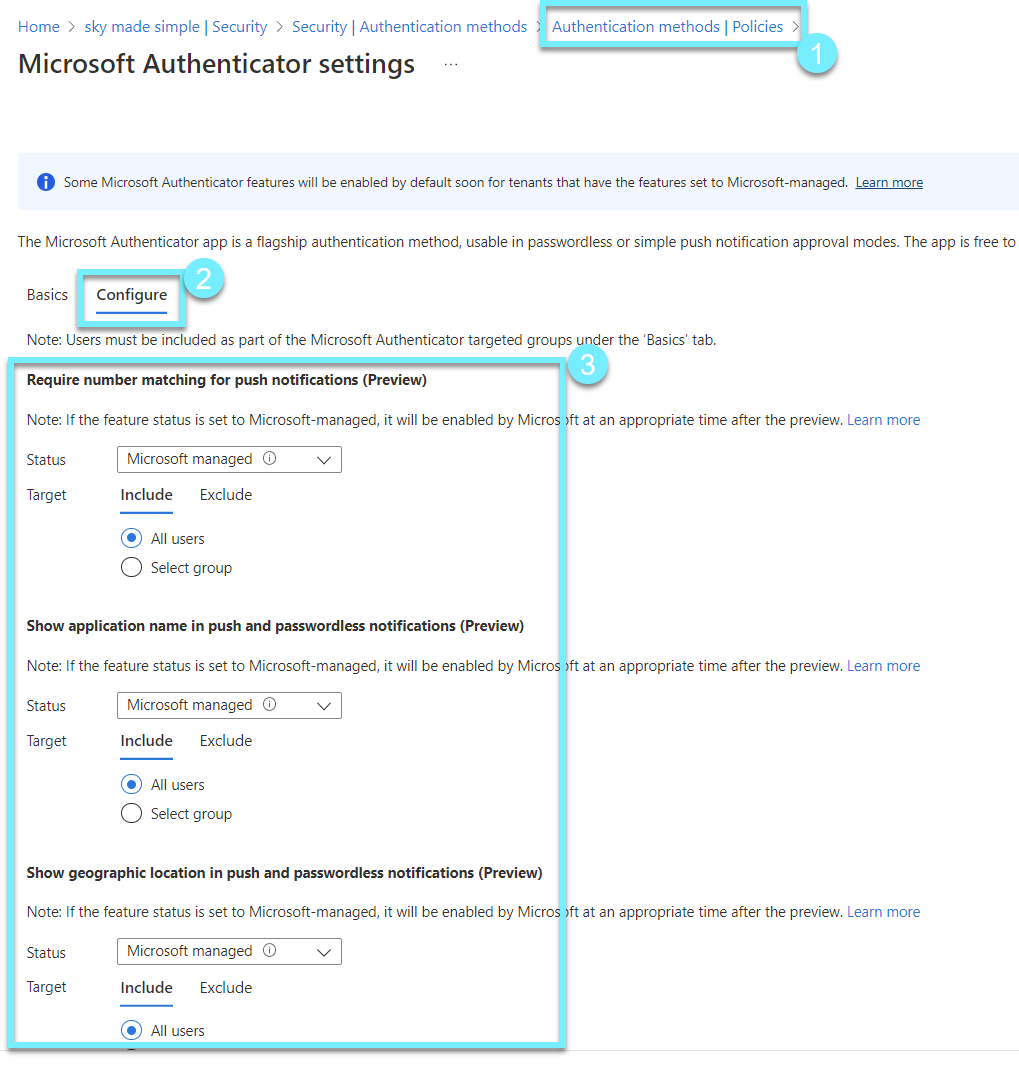
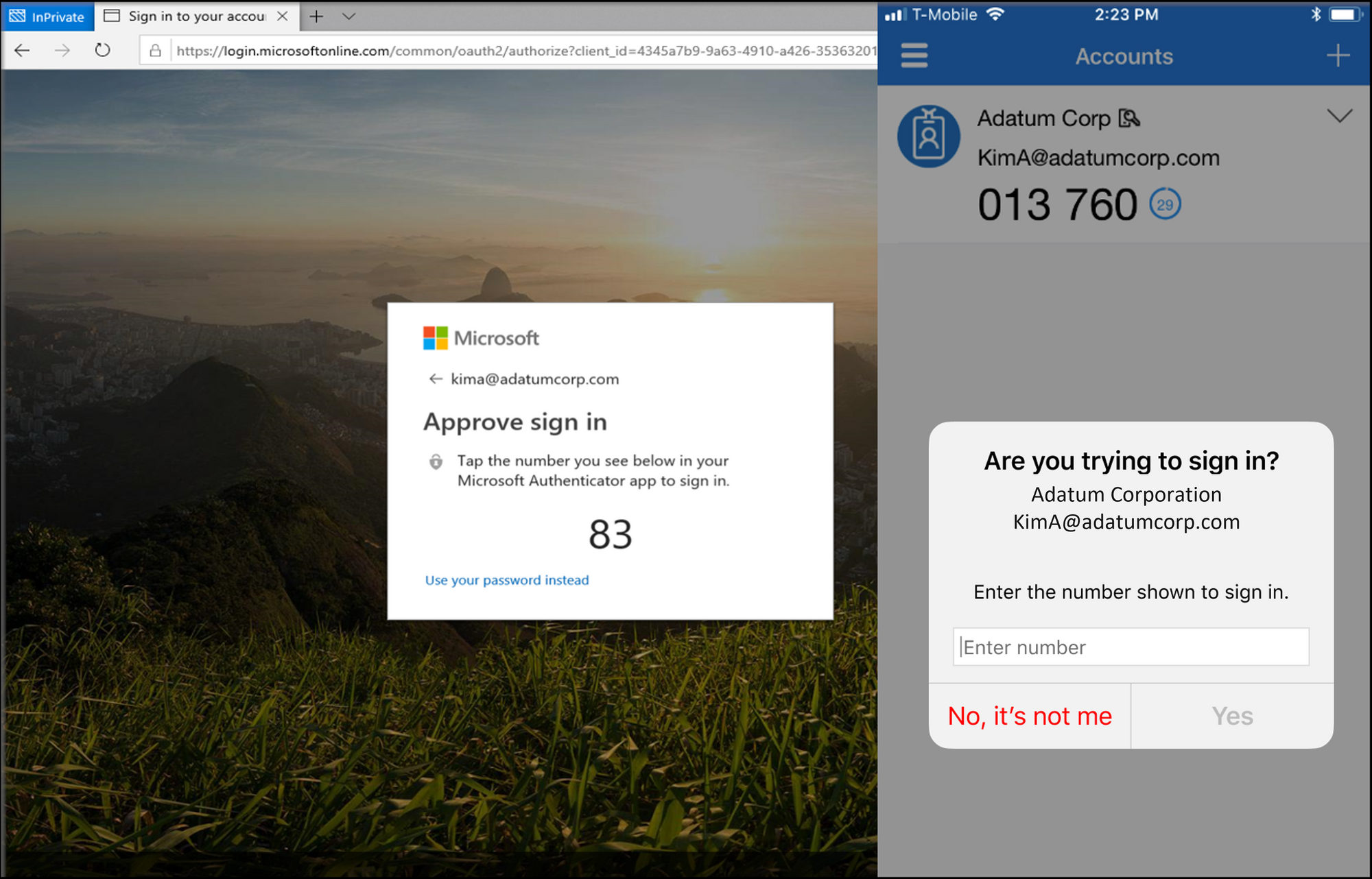
We are now able to do the following
- Prevent legitimate users from accidentally authorizing logins.
- Aid users in making reasonable decisions by providing more context.
What we are able to use is
- require number matching for push notifications,
- show application name in push and passwordless notification and
- show geographic location in push and passwordless notification.
All three solutions are designed to provide users with the proper context for signing in. My suggestion is to use "require number matching" which will eliminate many MFA fatigue attacks.
What you need to review
To avoid MFA fatigue, we must reconsider authentication methods and how we implement MFA. These factors are critical in ensuring that our users have the proper context when they approve their sign-in and only when necessary.
- Implement number matching
- Sign-in frequencies (SIF) on compliant devices from Conditional Access
- With Azure Identity Protection, rethink Sign-in frequencies and consider anomalies from cloud intelligence (Sign-in risk and User Risk)
- Trust Primary Refresh Token and try to comprehend their importance and ability to function under conditions that satisfy both IT and user functions.
- You can begin implementing Passwordless using "staged rollout."
More information